The SOC analyst job description has changed more in the past eighteen months than in the preceding decade. The traditional Tier 1 analyst — the person who sat in front of a SIEM dashboard, triaged alerts one by one, and escalated anything suspicious to a senior colleague — is being fundamentally reshaped by artificial intelligence. In its place, a new role is emerging: the AI SOC analyst job description reflects a professional who works alongside autonomous AI systems, supervising machine-driven triage, handling the complex investigations that AI escalates, and applying human judgment where machines cannot.
Whether you are a hiring manager writing a job specification, an IT leader trying to understand what capability you need, a career professional considering a move into this space, or a small business owner wondering whether you need to hire for this role at all, this guide provides the definitive AI SOC analyst job description for 2026 — including the practical alternative that allows small businesses to access the same capability through a managed service.
How AI Has Transformed the SOC Analyst Role
To write an accurate AI SOC analyst job description, you first need to understand what has changed and why.
The traditional SOC analyst role was structured in tiers. Tier 1 analysts handled initial alert triage — the high-volume, repetitive work of reviewing every alert generated by security tools and deciding whether each one warranted further investigation. Tier 2 analysts conducted deeper investigations on escalated alerts. Tier 3 analysts and threat hunters focused on advanced analysis, proactive threat hunting, and incident response.
This tiered model worked when alert volumes were manageable and the tools were simpler. In 2026, it has become untenable. Security tools generate tens of thousands of alerts per day in a typical mid-sized environment. Only 1–5% represent genuine threats. The rest is noise — but each alert still requires investigation to make that determination. Human Tier 1 analysts cannot process this volume with the speed and consistency required. The result is alert fatigue, missed threats, and analyst burnout.
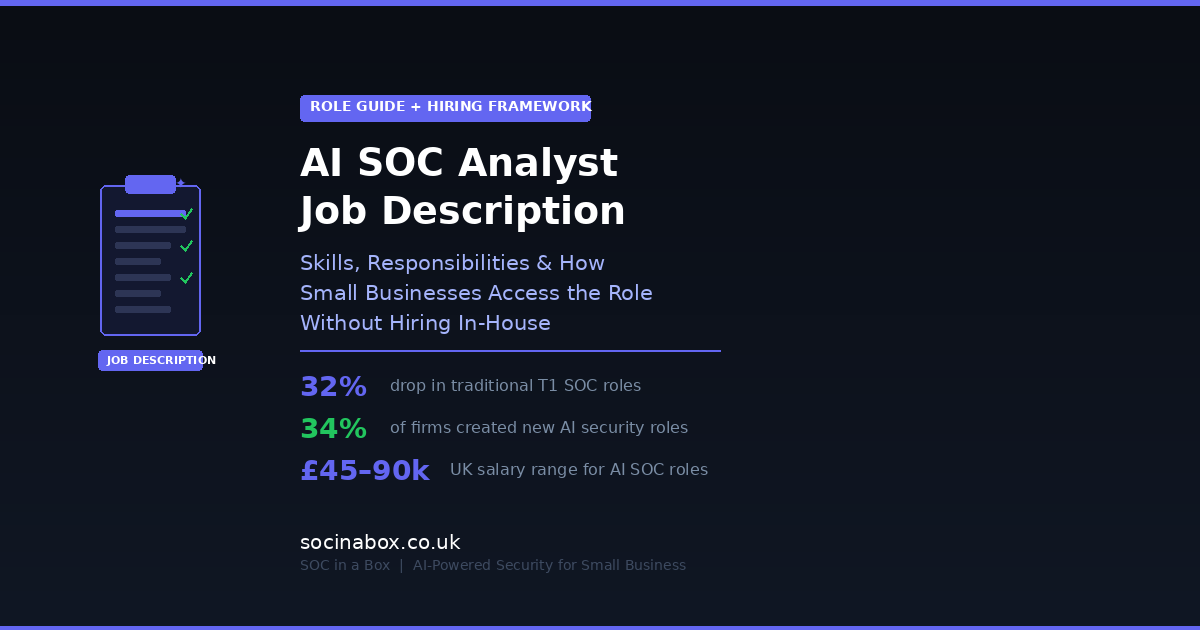
AI has stepped into this gap. The 2026 SANS Cybersecurity Workforce Report confirmed what production deployments have demonstrated: AI now autonomously resolves over 90% of Tier 1 alerts, covering triage, enrichment, categorisation, and initial containment. Entry-level SOC analyst positions have seen a 32% reduction as AI absorbs the routine analytical work that defined them.
But this is not a story of replacement — it is a story of elevation. The AI SOC analyst job description in 2026 describes a role that is more strategic, more technically demanding, and more valuable than the Tier 1 position it evolved from. The analyst becomes a supervisor, investigator, and threat hunter who works in partnership with AI rather than being replaced by it. For a broader look at how AI is transforming the Security Operations Centre as a whole, our guide to what a SOC is and why your business needs one provides the foundational context.
AI SOC Analyst Job Description: Core Responsibilities
The following AI SOC analyst job description reflects what leading organisations — including managed security service providers, enterprise SOCs, and AI-native security companies — are hiring for in 2026.
AI-Escalated Alert Investigation
The primary operational responsibility. When the AI triage engine identifies an alert as potentially malicious or too ambiguous to resolve autonomously, it escalates to the human analyst with a complete investigation package: the original alert, the tools queried, the evidence gathered, the reasoning behind the escalation, and recommended next steps.
The analyst reviews this package, applies business context the AI does not have, conducts additional investigation where needed, and reaches a final verdict. This is fundamentally different from traditional Tier 1 work — the analyst is not starting from a raw alert but from a pre-investigated case that requires human judgment to resolve. The quality of investigation is higher, the context is richer, and the decisions are more consequential than routine triage.
AI Supervision and Quality Assurance
A critical and entirely new dimension of the AI SOC analyst job description. The analyst monitors the quality and accuracy of AI-generated verdicts, identifies patterns of false negatives (genuine threats the AI missed) or systematic false positives (categories of alert the AI consistently misjudges), and provides feedback that improves the AI's models over time.
This supervisory function requires a different mindset from traditional alert triage. Rather than processing individual alerts sequentially, the analyst is evaluating the AI's analytical performance across hundreds or thousands of automated decisions, spotting trends, and making calibration recommendations. It demands both technical depth (understanding why the AI reached a particular conclusion) and statistical thinking (identifying patterns across large datasets of AI decisions).
Proactive Threat Hunting
With AI handling operational triage, the human analyst has capacity for proactive threat hunting — actively searching for threats that have evaded automated detection. This includes formulating hypotheses based on threat intelligence (for example: "a ransomware group is targeting UK professional services firms using a specific initial access technique — is there evidence of this technique in our environment?"), querying historical and real-time data to test those hypotheses, and investigating anomalies that do not match any known signature but exhibit characteristics consistent with adversary activity.
Threat hunting is the highest-value analytical work in a SOC. In the traditional model, it was perpetually deprioritised because Tier 3 analysts were pulled into operational firefighting. The AI SOC analyst job description in 2026 makes hunting a core responsibility rather than an aspiration, because AI has absorbed the operational load that previously consumed all available human capacity.
Incident Response Coordination
When a confirmed incident occurs, the AI SOC analyst coordinates the response — working with the AI to execute containment actions (isolating endpoints, blocking malicious traffic, disabling compromised accounts), communicating with stakeholders about the incident's scope and impact, preserving forensic evidence for potential legal or regulatory proceedings, and guiding the organisation through recovery. For managed service providers, this means coordinating directly with the client's leadership, explaining technical findings in business terms, and providing clear recommendations for immediate and longer-term action.
Threat Intelligence Operationalisation
The analyst translates external threat intelligence — from commercial feeds, government sources such as the NCSC, industry sharing groups, and dark web monitoring — into actionable detection logic. This might mean creating new detection rules based on newly published indicators of compromise, adjusting AI sensitivity for specific threat categories based on intelligence about active campaigns, or briefing clients on sector-specific threats that require heightened vigilance. Our dark web monitoring guide explains one of the key intelligence sources that feeds into this analytical work.
Client Communication and Reporting
In a managed SOC environment, the AI SOC analyst serves as the primary security interface for client organisations. This means translating technical findings into business language, producing clear monthly reports on threats detected and security posture, conducting periodic reviews to assess evolving risks, and building the kind of trusted relationship that makes security guidance actionable rather than abstract. The Confidence Score that SOC in a Box provides is one example of how this reporting is designed for business leaders rather than security engineers.
Continuous Improvement and Automation
The analyst identifies opportunities to expand AI automation — new alert categories that could be triaged autonomously, response actions that could be automated for specific threat types, and detection logic that could be enhanced based on observed attack patterns. This responsibility makes the AI SOC analyst a force multiplier: every improvement they implement increases the AI's capability, which in turn frees more human capacity for higher-value work.
Required Skills and Qualifications
The skills profile in the AI SOC analyst job description blends traditional security operations expertise with new competencies specific to AI-augmented environments.
Technical Skills
Security operations fundamentals. Understanding of SIEM, EDR, firewalls, intrusion detection, email security, identity management, and cloud security platforms. The analyst must be able to interpret alerts from all of these tools and understand the telemetry they produce. Experience with specific platforms — Microsoft Sentinel, Splunk, CrowdStrike, SentinelOne, Microsoft Defender — is typically expected.
Threat intelligence and frameworks. Familiarity with the MITRE ATT&CK framework, the Lockheed Martin Cyber Kill Chain, and structured threat intelligence methodologies. The analyst must be able to map observed activity to known adversary techniques and use frameworks to guide investigation and hunting.
AI and automation literacy. This is the new dimension. The analyst does not need to be a machine learning engineer, but they must understand how AI triage and investigation systems work at a functional level — what data they use, how they reach conclusions, what their limitations are, and how to interpret and quality-assure their outputs. Familiarity with concepts like agentic AI, large language models in security contexts, and explainable AI (XAI) is increasingly expected.
Scripting and query capability. Proficiency in at least one scripting language (Python is most common) and the ability to write queries in KQL, SPL, or equivalent SIEM query languages. The analyst uses these to conduct custom investigations, build detection rules, and extract data for threat hunting that goes beyond what the AI's standard capabilities cover.
Cloud security. With the majority of small and medium businesses operating in cloud and hybrid environments, practical knowledge of Microsoft 365 security, Azure/AWS/GCP security controls, and cloud-specific attack vectors is essential. Understanding how Microsoft 365 security works in practice is particularly relevant for the UK SMB market.
Network and endpoint forensics. The ability to conduct deep-dive forensic analysis when required — examining packet captures, process execution chains, registry modifications, file system artefacts, and memory dumps. While AI handles routine investigation, the analyst must be capable of hands-on forensic work for complex or novel incidents.
Soft Skills and Professional Qualities
Critical thinking and analytical judgment. The core value of the human AI SOC analyst lies in their ability to exercise judgment that AI cannot — assessing ambiguous situations, weighing business context against technical evidence, and making decisions in conditions of uncertainty. This demands rigorous analytical thinking rather than procedural compliance.
Communication. The ability to explain complex technical findings to non-technical audiences is essential, particularly in managed service environments where the analyst interfaces directly with client leadership. Written reporting must be clear, concise, and actionable. Verbal communication during incidents must be calm, authoritative, and free of unnecessary jargon.
Continuous learning orientation. The threat landscape, the tools, and the AI capabilities are all evolving rapidly. The analyst must be comfortable with continuous professional development, staying current with emerging threats, new AI capabilities, and evolving regulatory requirements.
Comfort with ambiguity. AI handles the clear-cut decisions. The cases that reach the human analyst are, by definition, the ones that are uncertain, complex, or novel. The analyst must be comfortable making decisions with incomplete information, documenting their reasoning, and adjusting their conclusions as new evidence emerges.
Certifications
Certifications commonly listed in the AI SOC analyst job description include CREST Certified SOC Analyst (CCSA) or CREST Practitioner Security Analyst (CPSA), CompTIA Security+ or CySA+ (Cybersecurity Analyst), GIAC Security Operations Certified (GSOC), Certified SOC Analyst (CSA) from EC-Council, and SANS certifications relevant to security operations and incident handling. Increasingly, certifications or demonstrated competence in AI governance (such as ISO 42001 awareness) and cloud security (such as Microsoft SC-200 or AWS Security Specialty) are differentiators.
UK Salary Benchmarks for 2026
Understanding the market rate is essential whether you are hiring, budgeting, or evaluating whether in-house recruitment makes financial sense for your organisation.
Junior AI SOC analyst (0–2 years experience): £35,000–£45,000. These roles are increasingly scarce as AI absorbs the entry-level triage work that previously defined them. Candidates at this level are expected to have foundational security knowledge, some hands-on experience (often from apprenticeships, graduate programmes, or adjacent IT roles), and demonstrable AI literacy.
Mid-level AI SOC analyst (2–5 years): £45,000–£65,000. The core of the market. These analysts have practical experience working in AI-augmented SOC environments, can supervise AI triage quality, conduct threat hunting, handle escalated investigations, and communicate effectively with clients or internal stakeholders.
Senior AI SOC analyst / threat hunter (5+ years): £65,000–£90,000. Experienced professionals who lead complex investigations, develop detection strategies, mentor junior analysts, contribute to AI model improvement, and provide strategic security guidance. Often hold multiple advanced certifications and have deep expertise in specific threat domains.
AI SOC team lead / manager: £80,000–£110,000+. Responsible for SOC operations strategy, AI governance, team performance, client relationships, and continuous service improvement. Combines deep technical expertise with leadership and business acumen.
These figures reflect the UK market in 2026 and vary by region (London commands a 15–25% premium over regional rates), sector (financial services and defence tend to pay above average), and the specific employer (managed service providers, in-house enterprise SOCs, and AI-native security vendors have different compensation structures).
Sample AI SOC Analyst Job Description
For hiring managers who need a ready-to-adapt template, here is a representative AI SOC analyst job description for a mid-level role in a managed SOC environment.
Role title: AI SOC Analyst
Reports to: SOC Manager / Head of Security Operations
Location: Remote / Hybrid (UK-based)
Role summary: Working within our AI-augmented Security Operations Centre, you will investigate security alerts escalated by our AI triage engine, conduct proactive threat hunting, coordinate incident response for client organisations, and contribute to the continuous improvement of our detection and response capabilities. You will serve as a named analyst for a portfolio of SMB clients, building trusted relationships and providing clear, actionable security guidance.
Key responsibilities: Investigate AI-escalated alerts, applying business context and human judgment to reach final verdicts on complex or ambiguous cases. Monitor AI triage quality, identifying patterns of false negatives or systematic misclassification and providing feedback to improve model accuracy. Conduct proactive threat hunting using threat intelligence, behavioural analysis, and hypothesis-driven investigation across client environments. Coordinate incident response for confirmed security events, including containment, forensic preservation, stakeholder communication, and recovery guidance. Operationalise threat intelligence from commercial, government, and open-source feeds into actionable detection logic. Produce clear, business-focused monthly security reports for client leadership. Contribute to detection engineering — developing, testing, and refining correlation rules and AI training data. Participate in continuous improvement initiatives, identifying opportunities to expand AI automation and improve service delivery.
Essential requirements: Minimum 2 years of experience in a SOC or security operations role. Practical experience working alongside AI triage or SOAR automation systems. Strong knowledge of SIEM, EDR, and cloud security platforms (Microsoft stack preferred). Familiarity with MITRE ATT&CK and structured threat intelligence frameworks. Proficiency in at least one scripting language (Python preferred) and SIEM query languages. Excellent written and verbal communication skills. Eligibility for UK security clearance if required by client contracts.
Desirable: CREST, GIAC, or CompTIA CySA+ certification. Experience in a managed security service provider (MSSP) environment. Familiarity with deception technology, dark web intelligence, and data loss prevention. Understanding of UK regulatory frameworks including GDPR, Cyber Essentials, and NIS2. Experience with AI governance principles and ISO 42001.
What This Means for Small Businesses
If you are a small business owner reading this AI SOC analyst job description, your reaction might be: "this is exactly the capability I need — but I cannot afford to hire someone with this profile." That reaction is entirely correct, and it points to the most important practical insight in this entire article.
Hiring a mid-level AI SOC analyst at £55,000 gives you one person covering business hours Monday to Friday. For genuine 24/7 coverage, you need four to five analysts — pushing your staffing cost alone to £220,000–£275,000 per year, before tools, management, and training. For a business with 20, 50, or even 200 employees, this is not a viable staffing model.
The managed SOC model exists precisely to solve this problem. When you engage a managed AI & SOC service, you are not hiring an individual — you are accessing a team of professionals matching the AI SOC analyst job description outlined above, supported by AI technology that multiplies their capacity, available around the clock, for a monthly fee that is a fraction of a single analyst's salary.
With SOC in a Box, your named analyst is a CREST-certified professional who matches this job description — they investigate escalated alerts, hunt for threats proactively, coordinate incident response, provide strategic guidance, and produce clear reporting for your leadership. Behind them, EmilyAI handles the AI triage and investigation throughput that would otherwise require a full Tier 1 team. DecoyPulse provides zero-false-positive deception detection. Dark web monitoring, attack surface management, and data loss prevention complete the picture.
The total cost: from £335 per month. For most small businesses, this is less than they currently spend on disconnected piecemeal security tools that provide a fraction of the capability.
Hiring vs Managed Service: A Decision Framework
Not every organisation should default to a managed service, and not every organisation should hire in-house. Here is a framework for making the right decision.
Hire in-house when: Your organisation has 500+ employees and generates sufficient alert volume and security complexity to justify dedicated staff. You operate in a regulated sector (financial services, defence, critical national infrastructure) where regulators may expect in-house security operations capability. You have the budget for not just the analyst but the full supporting infrastructure — SIEM, EDR, threat intelligence, and management oversight. You need staff with security clearance that cannot be delegated to an external provider. You can offer a career path that retains talent in a market where the average SOC analyst tenure is under two years.
Use a managed service when: Your organisation has fewer than 500 employees and cannot justify the cost of a full in-house SOC team. You need 24/7 coverage but cannot staff for it internally. You want to access AI-augmented security operations without building and managing the AI platform yourself. You prefer predictable monthly costs over the variable expense of recruitment, training, and retention. You need to be operational quickly — SOC in a Box deploys in five working days, versus the months it typically takes to recruit, onboard, and ramp a new analyst. Your security needs are real but your internal expertise is limited — you need a partner who provides both the technology and the human judgment.
Consider a co-managed model when: You have internal IT staff with some security capability but need specialist support for complex investigations and 24/7 coverage. You want to retain control over first-line response while accessing expert escalation support. Your compliance framework requires demonstrable internal security governance alongside external monitoring.
The Career Path: From Traditional Analyst to AI SOC Professional
For professionals considering a career move into this space, the AI SOC analyst job description represents both an opportunity and a challenge. The opportunity is clear: the role is more strategic, more intellectually demanding, and better compensated than the Tier 1 triage work it evolved from. The challenge is that the skills required are broader and more sophisticated.
The 2026 SANS Workforce Report found that while traditional entry-level SOC analyst roles have declined by 32%, entirely new roles have emerged: 34% of organisations have created AI/ML security specialist positions, 32% have added AI security engineering roles, and 30% have established AI governance analyst positions. The talent pipeline is being redirected, not eliminated.
For those building a career path, the practical priorities are as follows. First, establish strong security operations fundamentals — understanding of networks, endpoints, identity systems, cloud platforms, and common attack techniques. This foundation does not change regardless of how much AI is involved. Second, develop AI literacy — not at the level of building machine learning models, but at the level of understanding how AI triage systems work, what their limitations are, and how to evaluate their outputs critically. Third, invest in threat intelligence and hunting skills — these are the capabilities that AI augments but cannot replace, and they command the highest premium in the market. Fourth, build communication skills — the ability to translate technical findings into business impact is what makes an analyst valuable to the organisations they serve.
The NCSC's cyber careers resources provide a useful starting point for mapping qualifications and certifications to specific career goals within UK cyber security.
How the AI SOC Analyst Role Works Inside SOC in a Box
To make the AI SOC analyst job description tangible, here is how the role operates within our managed service — the model that small businesses actually interact with.
Your named analyst is a real person with a name, a direct contact method, and a relationship with your business. They are not a rotating shift worker in a call centre. They learn your network, your users, your business processes, and your risk profile. When EmilyAI escalates an alert, your analyst investigates it with full knowledge of your context — they know that your finance director works unusual hours, that your development team accesses staging servers from home, and that your office printer generates spurious network traffic every Tuesday morning.
This contextual knowledge is exactly what the AI SOC analyst job description demands: the ability to apply human judgment that AI cannot replicate. And in a managed service model, you get this capability without recruiting, training, or managing the person yourself — and without the risk of losing them to a higher bidder eighteen months later.
Behind the named analyst, the full SOC in a Box stack operates: the SOC365 detection engine for correlation and detection, EmilyAI for AI triage and investigation, DecoyPulse for deception-based detection, dark web monitoring for external intelligence, data loss prevention for insider threat detection, and attack surface management for continuous external visibility. Every capability described in the AI SOC analyst job description above is delivered through this integrated platform — at a cost that starts from £335 per month.
Frequently Asked Questions
Does an AI SOC analyst replace the traditional SOC analyst?
Not replace — transform. The routine triage work that defined the traditional Tier 1 role is now handled by AI. The human role has evolved into a more strategic position focused on complex investigation, threat hunting, AI supervision, and client communication. The work is harder, more varied, and more valuable.
Can a small business hire an AI SOC analyst directly?
Technically yes, but practically it rarely makes sense. A single analyst provides coverage only during business hours, the salary (£45,000–£65,000+) exceeds what most SMBs can justify, and you still need the AI platform, SIEM, EDR, and threat intelligence infrastructure for them to work with. A managed service provides the same capability — and more — at a fraction of the cost with 24/7 coverage.
What certifications should an AI SOC analyst hold?
CREST certification (CCSA or CPSA) carries the most weight in the UK market. CompTIA CySA+, GIAC GSOC, and EC-Council CSA are also widely recognised. Increasingly, cloud security certifications (Microsoft SC-200, AWS Security Specialty) and AI governance awareness are expected.
How does AI supervision differ from traditional alert triage?
Traditional triage processes alerts one at a time: read alert, investigate, decide. AI supervision evaluates the AI's performance across thousands of automated decisions: is it consistently accurate? Are there categories it mishandles? Is it adapting to new threat types? The mindset shifts from individual case processing to systems-level quality assurance.
What is the career outlook for AI SOC analysts?
Strong and improving. While entry-level triage roles are declining, demand for analysts who can work effectively alongside AI, conduct threat hunting, and provide strategic security guidance is growing rapidly. The SANS 2026 report found that demand for AI-related security specialist roles nearly doubled year-over-year.
Conclusion: The Role Has Changed — The Need Has Not
The AI SOC analyst job description in 2026 looks markedly different from the SOC analyst role of even two years ago. The mechanical triage work is gone, absorbed by AI that performs it faster, more consistently, and at a scale no human team can match. In its place is a role that demands sharper analytical judgment, broader technical knowledge, stronger communication skills, and the ability to work in partnership with autonomous systems.
For organisations that can afford to hire for this role, the talent exists — but competition is fierce, salaries are rising, and retention is a perpetual challenge. For the vast majority of UK small businesses, the managed service model provides a more practical, more cost-effective, and more reliable way to access exactly the same capability.
Whether you are hiring an AI SOC analyst or engaging one through a managed service, the fundamental need has not changed: your business generates security data that must be monitored, threats must be detected and investigated, and incidents must be responded to quickly and effectively. AI has transformed how that work gets done. It has not changed the fact that it must get done.
For small businesses, SOC in a Box delivers the complete AI SOC analyst job description — the AI, the analyst, the tools, and the process — as a single managed service. From £335 per month. Five days to live monitoring. One invoice.
Access an AI SOC Analyst Without Hiring One
SOC in a Box gives your business a named, CREST-certified analyst backed by EmilyAI, DecoyPulse, and eight years of production-proven detection. 24/7 coverage. From £335/month.
See plans and pricing