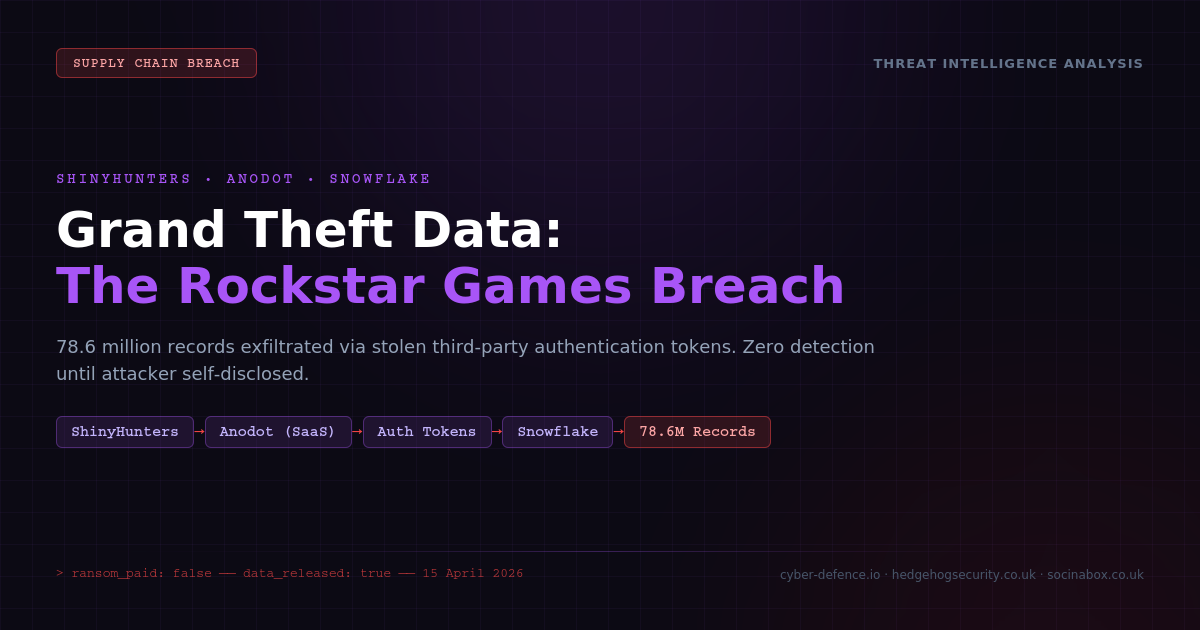
On 14 April 2026, the hacking group ShinyHunters released 78.6 million internal records stolen from Rockstar Games — the studio behind Grand Theft Auto, one of the most profitable entertainment franchises in history. The ransom demand went unpaid. The data is now public.
But the most important detail for every business owner is this: Rockstar's own systems were never directly attacked. The hackers broke in through a third-party cloud monitoring service that Rockstar trusted with access to its data. The breach happened through the supply chain — and that is a risk that affects businesses of every size.
What Happened
ShinyHunters — a well-known hacking group active since 2020 — did not attack Rockstar Games directly. Instead, they targeted Anodot, a cloud cost monitoring service that Rockstar used to track spending across its cloud infrastructure. Anodot, like many business analytics tools, needed access to Rockstar's cloud data warehouse (hosted by a company called Snowflake) to do its job.
The attackers broke into Anodot's systems and stole the authentication tokens — essentially digital keys — that Anodot used to connect to its customers' cloud environments. With those keys, ShinyHunters walked straight into Rockstar's data warehouse, appearing to Rockstar's security team as perfectly normal, authorised traffic. No alarms went off. No passwords were cracked. The attackers simply used a trusted door that someone else had left open.
On 11 April, ShinyHunters posted a ransom demand on their dark web site, giving Rockstar until 14 April to pay. Rockstar declined — in line with guidance from the UK's National Cyber Security Centre and law enforcement worldwide, which consistently advises against paying ransoms. On 13 April, ShinyHunters released the data early, taunting Rockstar publicly.
What Was Stolen
The leaked data consists of internal business analytics — not player accounts, passwords, or game development files. According to reports, the 78.6 million records include revenue figures for GTA Online and Red Dead Online, weekly sales data for in-game purchases, player activity metrics broken down by platform, and internal business intelligence used to monitor game performance.
Rockstar confirmed the breach, stating that "a limited amount of non-material company information was accessed" and that the incident had "no impact on our organisation or our players."
While this data may not seem sensitive at first glance, it reveals detailed financial and operational information that competitors, investors, and the public were never meant to see. For Rockstar, the reputational damage and the loss of commercially sensitive information is significant — even without a single player password being compromised.
This Is Not Just a Rockstar Problem
Here is why this matters for your business: Rockstar is not the only victim. ShinyHunters used the same Anodot breach to steal data from over a dozen companies simultaneously. In March 2026, the same group claimed to have obtained data from more than 400 companies through compromised Salesforce integrations using a near-identical technique.
The pattern is always the same: rather than attacking each company directly, the hackers compromise a shared third-party service that many companies trust with access to their data. One breach at the service provider becomes a breach at every company connected to it.
If you use any cloud-based service that connects to your business data — an accounting platform, a CRM, an analytics tool, a marketing automation system, a payroll provider — you have the same type of risk. The question is not whether your own systems are secure. The question is whether every service you have granted access to your data is equally secure.
What This Means for Small Businesses
You might think that supply chain attacks only target large enterprises. But the tools and services that were compromised in this campaign are used by businesses of all sizes. Cloud analytics platforms, CRM systems, and monitoring tools serve small businesses just as much as they serve global studios. If your cloud provider is breached, the size of your company is irrelevant — your data is equally exposed.
The specific risks for small businesses include the loss of customer data (triggering ICO reporting obligations under UK GDPR), exposure of financial records and supplier contracts, reputational damage that smaller businesses may struggle to recover from, and the potential for follow-on attacks using stolen credentials or business information.
What You Should Do
1. Know what is connected to your data. Make a list of every third-party service, app, or platform that has access to your business data. This includes your accounting software, CRM, email marketing tools, cloud storage, HR systems, and any integrations between them. If you are not sure what has access, that is itself a problem. Our security assessment service can help you map this.
2. Review permissions. For each connected service, ask: does it need all the access it has? A cloud cost monitoring tool does not need access to your entire data warehouse. A marketing platform does not need access to your financial records. Apply the principle of least privilege — every service should have the minimum access required to do its job, and nothing more.
3. Rotate your keys. Authentication tokens, API keys, and integration passwords should be changed regularly — not left in place indefinitely. If a token is stolen, rotation limits the window of exposure. Many cloud platforms allow you to set automatic token expiry.
4. Enable multi-factor authentication everywhere. Snowflake's 2024 breach campaign targeted accounts that did not have MFA enabled. Ensure that every cloud service your business uses requires multi-factor authentication, including for service accounts and integrations where possible.
5. Ask your suppliers about their security. You have every right to ask your cloud providers and SaaS vendors about their security practices. Do they conduct regular penetration testing? Do they have incident response plans? Do they notify you promptly if they suffer a breach? If they cannot answer these questions, that tells you something important. Our blog regularly covers how to evaluate vendor security.
6. Do not pay ransoms. Rockstar refused to pay, consistent with global law enforcement guidance. Paying a ransom provides no guarantee that data will be deleted, funds criminal operations, and makes your organisation a more attractive target for future attacks. The right approach is containment, investigation, and notification.
The Bigger Picture
The Rockstar Games breach is a high-profile example of a risk that every business faces in 2026. As businesses rely on more cloud services and third-party integrations, the attack surface expands beyond what any single organisation can directly control. Your security is now a shared responsibility — and your weakest vendor is your weakest link.
The good news is that the basic mitigations — knowing what is connected, applying least-privilege access, rotating credentials, and requiring MFA — are practical, affordable, and effective. They do not require a Rockstar-sized budget. They require attention and discipline.
Not Sure What Has Access to Your Data?
Our security assessments map your third-party integrations, identify over-permissioned services, and give you a practical plan to reduce your supply chain risk. It is the single most impactful step you can take after reading this article.
View our security packages